Cloud Imperium Games experienced a security breach in January that exposed limited user metadata and personal details, but no financial or sensitive data, with concerns raised about delayed breach notification and transparency under GDPR regulations. The video emphasizes the potential risks of exposed metadata, critiques CIG’s communication approach, and advises users to stay vigilant against phishing and social engineering threats.
In this video, the presenter discusses a security breach that Cloud Imperium Games (CIG), the developer behind Star Citizen, experienced back in January. The breach involved unauthorized access to some backup systems, resulting in limited access to users’ personal data such as metadata, contact details, usernames, dates of birth, and names. CIG responded promptly by containing the breach, blocking further unauthorized access, refreshing security settings, and assuring users that no financial or payment information, passwords, or sensitive data were compromised. The access was read-only, with no data modification or injection reported.
The presenter then explores the implications of this breach in relation to the European Union’s General Data Protection Regulation (GDPR). According to GDPR Article 33, organizations must notify data protection authorities within 72 hours of discovering a breach, especially if it poses a high risk to individuals’ rights and freedoms. While CIG stated that this incident does not pose such a risk, the presenter notes that the breach notification to users was delayed by over a month, raising questions about compliance and transparency. It is unclear whether CIG reported the breach to the relevant authorities or users in a timely manner, and the presenter highlights the complexity of GDPR requirements depending on the organization’s operations and data flows.
A key concern raised is the ambiguous nature of the “metadata” that was accessed. Although financial data was not involved, metadata could include information such as organizational affiliations, ship inventories, or spending habits within the game. Such data could potentially be exploited to identify high-value players (“whales”) or reveal private affiliations, which might lead to privacy violations or targeted harassment. The presenter emphasizes that even non-financial data can be sensitive and used for social engineering or other malicious activities, especially given the passionate and sometimes contentious Star Citizen community.
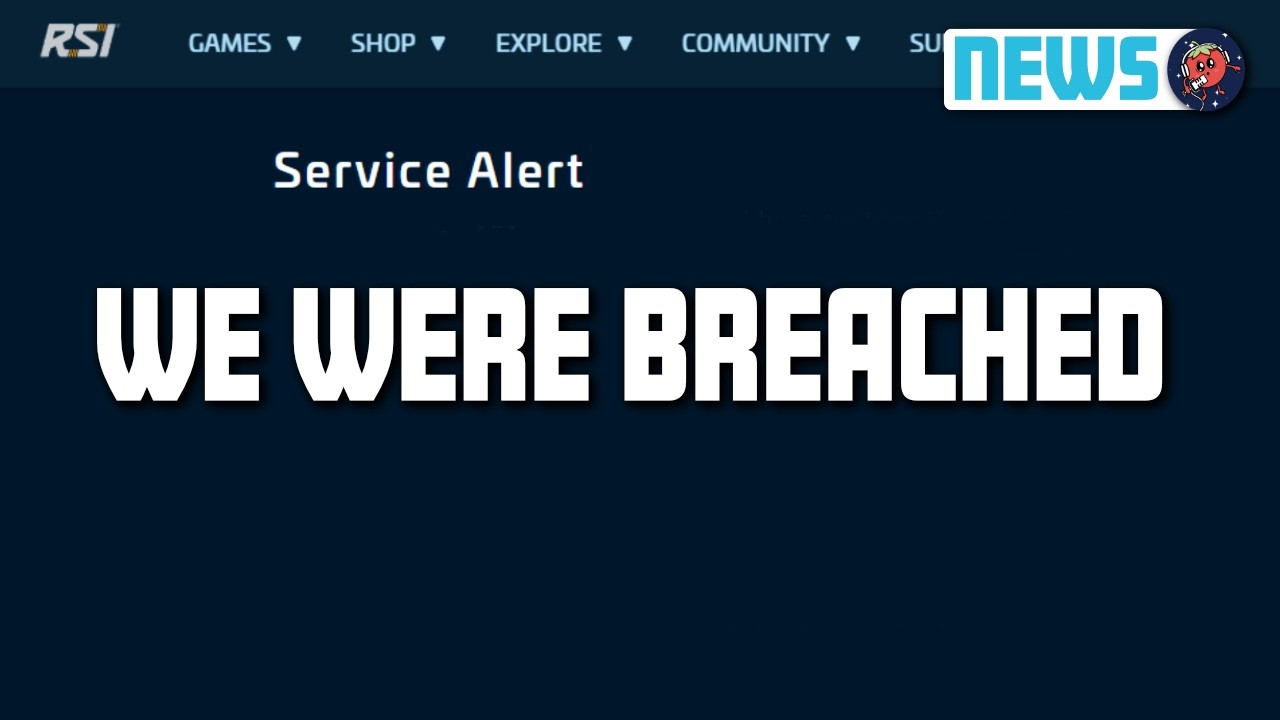
The video also critiques how CIG communicated the breach, noting the lack of prominent notification on their official website or community platforms like Spectrum. The announcement appears to have been quietly posted in less visible locations, which may reflect an attempt to minimize attention or public concern. The presenter suggests that this lack of transparency could undermine trust and leaves many questions unanswered about the full scope and impact of the breach. They express hope that CIG is handling the situation responsibly but acknowledge that detailed information might never be fully disclosed.
Finally, the presenter advises viewers to remain vigilant against phishing and social engineering attempts that could arise from leaked data. They recommend using two-factor authentication, verifying communications carefully, and avoiding clicking on suspicious links. The breach serves as a reminder of the importance of cybersecurity awareness, especially for those involved in online communities and gaming platforms. The video concludes with a call for caution but does not condemn CIG, instead encouraging users to stay informed and cautious in the wake of the incident.